SE::Google::Compromised - Checking for the "This site may be hacked" label in Google
Overview of the parser
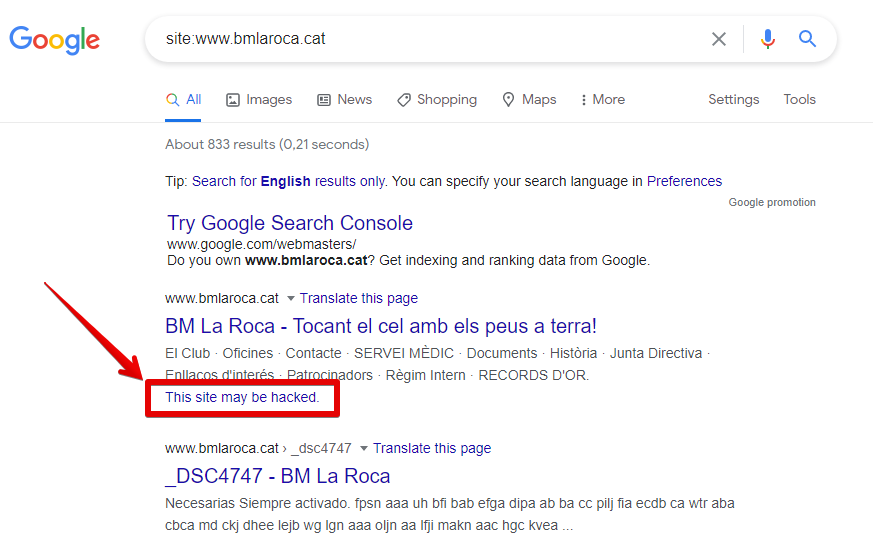
The Google Compromised parser allows you to check for the presence of the This site may be hacked label in Google search results. Using the Google Compromised parser, you can check your own domain databases for this label. You can learn more about this label in Google Search Help.
A-Parser functionality allows you to save parsing settings for future use (presets), set parsing schedules, and much more.
Saving results is possible in any form and structure you need, thanks to the built-in powerful Template Toolkit template engine, which allows you to apply additional logic to the results and output data in various formats, including JSON, SQL, and CSV.
Collected data
- Checking for the presence of the This site may be hacked label in Google
Capabilities
- Supports all features of the
 SE::Google parser.
SE::Google parser.
Use cases
- Checking a list of domains for the presence of the This site may be hacked label in Google
- Monitoring your own domains
Queries
You should specify the URL of the site you are looking for as queries, for example:
http://a-parser.com/
http://www.yandex.ru/
http://google.com/
http://russbehnke.com/
http://www.bmlaroca.cat/
http://vk.com/
http://facebook.com/
http://youtube.com/
Query substitutions
You can use built-in macros to automatically substitute subqueries from files; for example, if we want to check sites/a site against a keyword database, we specify several main queries:
ria.ru
lenta.ru
rbc.ru
yandex.ru
In the query format, we specify a macro for substituting additional words from the Keywords.txt file; this method allows checking a database of sites against a database of keywords and obtaining positions as a result:
$query {subs:Keywords}
This macro will create as many additional queries as there are in the file for each original search query, which in total will result in [number of original queries (domains)] x [number of queries in the Keywords file] = [total number of queries] as a result of the macro's operation.
You can also specify a protocol in the query format so that only domains can be used as queries:
http://$query
This format will prepend http:// to each query.
Output results examples
A-Parser supports flexible result formatting thanks to the built-in Template Toolkit template engine, which allows it to output results in an arbitrary form, as well as in a structured one, such as CSV or JSON
Exporting the list of label presence checks
Result format:
$query: $compromised\n
Example result showing the URL and the presence of the This site may be hacked label in Google:
http://a-parser.com/: 0
http://www.bmlaroca.cat/: 1
http://russbehnke.com/: 0
http://www.yandex.ru/: 0
http://google.com/: 0
Links + anchors + snippets with position output
Outputting links, anchors, and snippets to a CSV table
Saving related keywords
Keyword competition
Link indexing check
Saving in SQL format
Dumping results to JSON
Results processing
A-Parser allows processing results directly during parsing; in this section, we have listed the most popular cases for the SE::Google::Compromised parser
Saving domains with validation value "1"
Add a filter and select the validation value variable $compromised - Is site compromised from the drop-down list. Select type: String equals. Next, in String, enter the value we need: 1. With such a filter, you can remove all results with an unnecessary value.
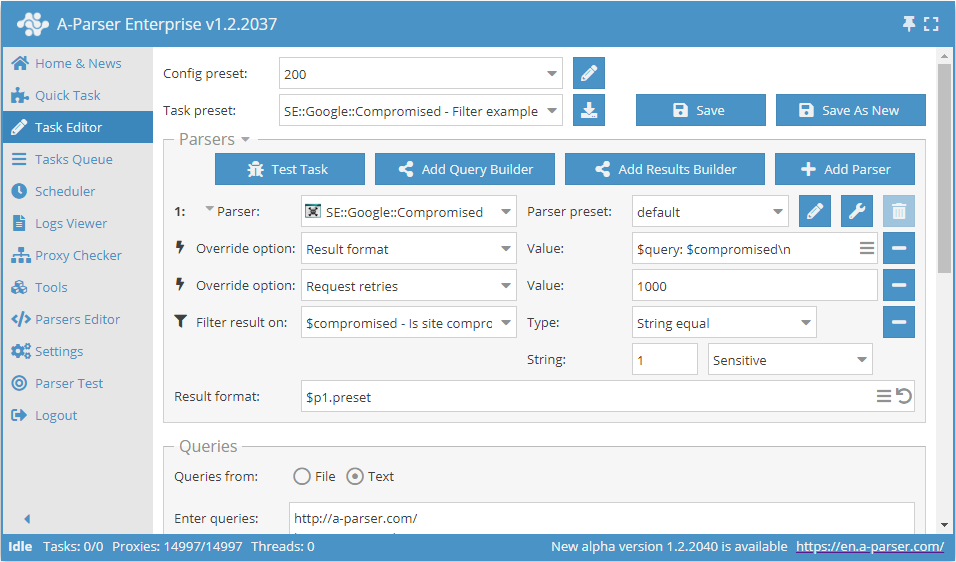
Download example
How to import an example into A-Parser
eJx1VE1z2jAQ/SseTQ7tDDFw6MU3woROOzSkITkBB2GtiYosCUnmYzz8965kYxta
btZ+vH37dtclcdRu7asBC86SZFESHb5JQubPSfJdqY2AJBmrXBuVcwsseowmXDgw
ERxprgWQHtHUWDA+f3EvDaMYZLQQjvRK4k4asITagzGceQjO8J0pk1OHBEIY2VNR
+LCHXQHmlEQPaYu3XEpyvo+EYceTAWc42A7ScDAYdNOy0AkG1DUTkl5RrvzvVTDs
Ciq6YPittONK4sOCtOS8Wl2g7CT04tnrYVyL2jjndA/vqiIArRmFhReah54ZdeC9
cSXKl6+xO3oEyhj3NamoKnjV26ofku8COakw1uuGAkywITQ5CABBzAu7RS0uQYgi
5P6uckiSUWGhRyxSnVAkwm49HKWhTplZ0ADtJVFyJMQU9iDasID/VHDBcEVGGSb9
qBP/HzL7B+PctNcthRM/GOTQoITX0+xXm8XUVG2wc7bGvgXPucO3HatC+sEM0LgF
0I1mL16zXBloytTIdXU8Ew3Sr1c7spFuTVdtXI3l2pgqmfHNrF7ZS2Qh3/EWZ9If
jQDflyyEwLFYeGvXY2TrMfhHS/A2eRxK+NYvR0ecUsL+nFdUteG4ft88wRyV7Fat
IVMqxMfbtOsh7Urh49M5nfT79LG6/hgvpx9FS1nbD4dDfKKSwTE2RdexCT+H23BT
WLuGT7mtPFcw61xQo1Iap9T1iafmYKNwaVG486r5/TR/sfLuTygpz7gWf+xrleE1
9PFow2HYcMnD81/p/MfQ
See also: Results filters
Link deduplication
Link deduplication by domain
Extracting domains
Removing tags from anchors and snippets
Filtering links by inclusion
Possible settings
Supports all settings of the  SE::Google parser, as well as additionally:
SE::Google parser, as well as additionally:
| Parameter name | Default value | Description |
|---|---|---|
| Pages count | 1 | Number of search result pages to parse (from 1 to 10) |